Short Introduction to DNS (switch to a Long DNS explanation)
Devices connected to the Internet are assigned unique numbers called IP addresses. You know this site as RouterSecurity.org and its IP address is 216.92.136.14. All communication on the Internet is based on these unique numbers, website names and computer names are just a convenience. The system that translates names into the underlying numeric IP addresses is called DNS (Domain Name System) and the computers that do the translation are referred to as DNS servers.
DNS Servers are extremely important. Probably 99% of all communication between two computers on the Internet, starts with a call to a DNS Server to translate a computer name into an IP address.
Malicious DNS servers can do what any malicious translator can do - lie to you. For example, they might send you to a scam copy of a website. Like food, you should not take DNS servers from a stranger.
You can check a computer or router to see what your DNS servers should be, but the pages below show what they actually are (with the tested web browser). That is, they report the DNS servers your current browser is actually using. We need tests like these because there are many places that DNS servers could have come from. The most recent change is that web browsers can now specify their desired DNS server.
The tests below run in a web browser. If one browser is using encrypted DNS while another, on the same computing device, is not, then expect these tests to show different results in each browser. Likewise, if you have two web browsers using different DNS providers, expect them to report different results in the tests below. For more on encrypted DNS see the Encrypted DNS topic on my Defensive Computing Checklist site.
I have a list of suggested DNS providers.
NOTE: If you are using the Private DNS feature of Android (first introduced in version 9) there is no need for any of the testers below. Android will always use the Private DNS servers, even when a VPN is active. Thank you, Google.
Learn Your Current DNS Servers
- DNS Leak Test is sponsored by VPN provider IVPN. It offers a quick standard test and a slower extended test. Both report the IP address, Hostname, ISP, City and Country for each detected DNS server. The initial screen shows your public IP address and location. (last verified Sept 2021)
- At browserleaks.com/ip you may need to scroll down to see a gray "Run DNS Leak Test" button. Click it. It reports the IP Address, ISP, city and country of the detected DNS servers. It does not report DNS server hostnames. Nice thing about this is that you can see both the public IP address and the DNS server IP address(es) right next to each other. The page also shows lots of other useful information. (last verified Sept 2021)
- The website dnscheck.tools was created in December 2021 by Reddit user dnschecktool. Initially it reports the ISP of the detected DNS server(s), the Advanced tab has many more details. No ads. No tracking. On a computer using OpenDNS, some of the detected DNS server names ended with strln.net. The domain belongs to Cisco which owns OpenDNS.
- DNS Leaktest from VPN provider Perfect Privacy reports the IP address, host name, ISP and country for each detected DNS server. It does not report the state or city where the DNS server is located. (last verified Sept 2021)
- dnsleak.com is sponsored and operated by Kape Technologies, the company that owns VPN provider Private Internet Access. It reports the IP address, hostname, city/region, country and ISP for each detected DNS server. (last verified Sept 2021)
- DNS Leak Test from VPN provider ExpressVPN reports the IP address, "Provider" and Country for each detected DNS server. It does not report a hostname or city. Note that it always warns that "DNS requests exposed!" which really means you are not connected to ExpressVPN. (last verified Sept 2021)
- Quad9: has their own DNS tester page. This is the result when the browser is using Quad9. They also have detailed explanations on how to confirm the use of Quad9 in Windows, macOS and Linux. These write-ups include operating system level tests.
(last verified July 2023)
- Cloudflare has a tester page at cloudflare-dns.com/help. A more memorable URL that also works is
1.1.1.1/help. The most important thing these report are "Connected to 1.1.1.1" which is YES/NO. If you are using Cloudflare, it shows the status of DNS over HTTPS and DNS over TLS. The "AS Name" identifies the ISP of your DNS provider. These pages also test the ability of your computer to connect to 1.1.1.1 and 1.0.0.1 and their IPv6 siblings.
Note that these tester pages are only interested in Cloudflare. When it says that neither DoH nor DoT is being used, that means they are not being used with Cloudflare. A web browser that is using DoH or DoT with another DNS provider, will be reported as not using DoH or DoT.
As detailed on the suggested DNS providers page, Cloudflare offers three DNS services: unfiltered, malware blocking and Family which blocks both malware and porn.- Verify that the malware blocking is working at phishing.testcategory.com. If the page displays at all, it is NOT working.
- Verify that the porn blocking is working at nudity.testcategory.com. If the page displays at all, it is NOT working.
- Screen shots: If phishing is allowed, you will see this page. If phishing is blocked you will see this in Brave or this if using Opera.
Want more? Cloudflare also provides www.cloudflarestatus.com which reports the overall status of their service. Ironically, if their service is down, it will block their users from seeing this website. You can not access cloudflarestatus.com by IP address. I tried. - OpenDNS: If you are using OpenDNS, you can verify this at www.opendns.com/welcome/. Rather than show all detected DNS servers, it simply reports a YES/NO status on whether OpenDNS is in use. (last verified July 2023)
- NEXTDNS (topic last updated March 26, 2023
The NextDNS tester page is: test.nextdns.io. Their documentation is scarce, so most of the below are just my observations.
A status of "ok" means that NextDNS is being used. A status of "unconfigured" means it is not being used. From here
When not in use, the only fields displayed are "resolver" (an IP address), "srcIP" and "server" (a name).
When NextDNS is being used there are multiple options: it could be used with secure encrypted DNS (DoH or DoT) or with old insecure DNS. Regardless of how you connect to NextDNS, their service might be used with your account and one of your profiles, or without your account. Even without an account, NextDNS still offers ad and tracker blocking, just not in the customized manner that having an account allows.
WORST CASE: When NextDNS is being used with old insecure DNS and without any of your profiles, the result looks like this
"status": "ok",
"protocol": "UDP",
"client": "1.2.3.4",
"srcIP": "1.2.3.4",
"destIP": "45.90.28.77",
"anycast": true,
"server": "zepto-ams-1",
"clientName": "unknown"
The "protocol" value of UDP is what indicates that secure encrypted DNS is not being used. Old DNS uses UDP, new DNS uses TCP. When encrypted DNS is used, the protocol will be either DOH or DOT. In the above, 1.2.3.4 represents your public IP address (if connected to a VPN, it is the IP address of the VPN server). "destIP" is the IP v4 address of a NextDNS DNS server.
ONE STEP UP: When NextDNS is being used with old insecure DNS but also with one of your account profiles, the result looks like this:
"status": "ok",
"protocol": "UDP",
"profile": "xxxxxxxxxxxxxxxxxx",
"client": "1.2.3.4",
"srcIP": "1.2.3.4",
"destIP": "45.90.28.77",
"anycast": true,
"server": "vultr-sea-1",
"clientName": "unknown"
The important difference is the presence of the "profile". The character string displayed here is not the same as that shown on the NextDNS website, so I don't know how to figure out which specific profile NextDNS is using.
I ran into this case when using a VPN that offered a Custom DNS option that only supported an IPv4 address (Mullvad on Windows). I set the Custom DNS IP address to one provided by NextDNS for my profile (on the NextDNS website) and then told NextDNS to use that profile with the pubic IP address of one specific VPN server (on the website this is the "Linked IP"). This also required that the browser used for the test was not configured to use secure DNS. This is a fragile setup, as it breaks when you connect to any other VPN server.
BEST CASE: When NextDNS is being used securely and with one of your profiles, the result looks like this
"status": "ok",
"protocol": "DOH",
"profile": "xxxxxxxxxxxxxxxxxx",
"client": "1.2.3.4",
"srcIP": "1.2.3.4",
"destIP": "149.248.36.234",
"anycast": false,
"server": "vultr-sea-1",
"clientName": "unknown-doh",
"deviceName": "MikeyFirefox",
"deviceID": "xxxxx"
A "protocol" value of DOH (for DNS over HTTPS) indicates that secure encrypted DNS is being used. A value of DOT also means that secure DNS is being used. Here, again, 1.2.3.4 represents your public IP address. The "destIP" is the DNS server IP address. The one in the example (149.248.36.234) is in Seattle. This should be physically close to your location when not using a VPN, and close to the VPN server when connected to a VPN. The "server" is the name of the DNS server being used.NextDNS seems to include a location indicator in the server name. In the example above, "sea" is probably for Seattle.
NextDNS lets you have multiple devices in a single profile and give a name to each device which makes it easy to distinguish one device from another in the logs. That said, a device is not a device, as three different browsers on the same computer can have three different DNS profiles. In the above, the "deviceName" is "MikeyFirefox". That copy of Firefox was configured with this DNS server name
https://dns.nextdns.io /xxxxxx/ MikeyFirefox
where the Xs represent a specific NextDNS profile of mine (the spaces are only there due to page formatting quirks in some browsers). The Chrome browser on the same computer, could have a different device name. Note that Chrome also uses DoH, so the format of the DNS server name in the Chrome settings is the same as shown above. I don't know what to make of the "deviceID", the "profile" or the "anycast" value of true or false.
The NextDNS website can also serve as a DNS tester. From the home page, click the blue button that says "Try it now". If NextDNS is being used, near the top of the resulting page it will say either "All good! This device is using NextDNS with this configuration" or "This device is using NextDNS with another profile." Note that these messages do not imply that either DoH or DoT are being used. NextDNS is just as happy to use old, insecure, UDP-based DNS. If NextDNS is not being used, the page will say: "This device is not using NextDNS. This device is currently using xxxxxx as DNS resolver". Note that these messages are poorly worded. The test does not apply to an entire device system wide, it is only valid for the web browser currently being used. For more detailed results, log into the NextDNS website from whatever browser you which to test. - The Mullvad connection check page has four big buttons that are either red or green. One is for DNS. If you are not connected to the Mullvad VPN, it will say that you are leaking DNS servers. Still, it is useful to everyone, not just Mullvad customers. Click on the downward pointing arrow on the DNS button to see the IP address, ISP/Provider and the location (in the US, it shows the City and State) of the detected DNS server(s). If you are connected to the Mullvad VPN, then it also shows the server name. Note that if you are using their Secure DNS service without their VPN, it will show in green and say that DNS is not leaking. (last verified December 2022)
- If you use AdGuard for DNS, their overview page includes a tester and will confirm/deny the use of their service. It is in the middle of the page, look for "AdGuard DNS servers map" If not using their service, it says "You are currently not using AdGuard DNS" In addition they have a dedicated tester page that tests both for their DNS service and for other software of theirs. (last verified Sept 2021)
- The Tenta VPN tester reports the IP address, ISP, and the city, state and country for detected DNS servers. It does not show the hostname. If you click the link to the Advanced Test results, then it also shows a whole host of advanced data about each DNS server. The meaning and importance of this data is beyond me (and not explained). The test may be buggy, I once saw the same DNS server IP address listed eight times. (last verified Sept 2021)
- ipx.ac is from VPN provider VPN.ac. Click the big orange button to "Test for leaks and footprints" at the bottom of the page to see the IP address, country and ISP of detected DNS servers. It does not show the names of each DNS server. The page tests much more than just DNS. (last verified Jan. 2022)
- whatsmydnsserver.com is from the people that gave up top10vpn.com. It reports the IP address, ISP and Country where your DNS server lives. It does not report the DNS server name. The explanation of DNS on the page is awful. (last verified Jan. 2022)
- The F-Secure Router Checker does not really check routers, it simply reports on a DNS server (IP address, ISP and country). The company says their goal is to insure that your router is using an "authorized DNS server" but there is no such thing and they don't define it. (last verified Sept 2021)
- ipleak.net is from VPN provider AirVPN. For each DNS server, it reports the IP address and location. No ISP or DNS server hostname. It also reports on other things such as WebRTC, IPv6 and your screen resolution. This is my least favorite option as the font used for the IP addresses is all but unreadable. It is also available on ports 8000 and 62222.
OPERATING SYSTEM TESTS
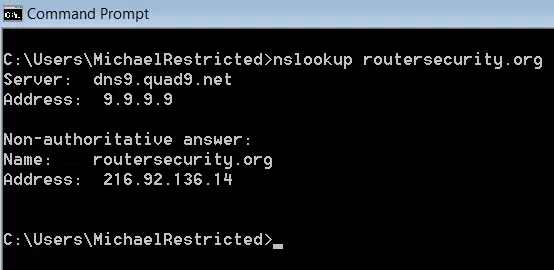
To see what the Operating System is using for DNS, outside of any web browsers, we can use the nslookup command on desktop operating systems (Windows, macOS, Linux). The command syntax is very simple: "nslookup domainname". The first thing returned by the command is the name and IP address of the default DNS server. Below is a screen shot from Windows 7 showing the system is using DNS server dns9.quad9.net at IP address 9.9.9.9.
DNS configurations in the Operating System can be all over the map. There can be different DNS servers configured for Ethernet vs. Wi-Fi. And, each wireless network (SSID) can be configured to use different DNS servers. Android 9, 10, 11 and 12 allow a global DNS setting for the entire operating system. iOS is the exact opposite, it even allows each app to configure its own DNS servers.
If a specific network connection does not specify any specific DNS server(s), then it gets assigned DNS servers by the router. But, again, a complication. The router may function as a DNS server itself, or it may simply pass DNS requests out to a DNS server on the Internet.
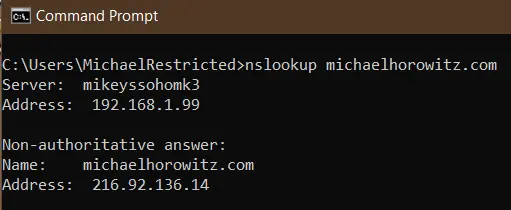
In the example above, the network connection was specifically configured to use Quad9. In the example below, a Windows 10 computer is using the router itself (at 192.168.1.99) as the DNS server.
FYI: On Windows, there are a couple debug options for the nslookup command. More here: nslookup's Debug Options by Didier Stevens (May 5, 2024).
Another option for Windows users is the ipconfig command. Its equivalent for MacOS and Linux is ifconfig.
On Windows, the command ipconfig /all shows details, including the DNS server(s) for all the defined network connections. Note that this only applies to the old insecure version of DNS. It does not know about browsers using new secure DNS. And, what the operating system specifies for old DNS can be transparently over-ridden by the router. Also, when connected to a VPN, there will be one entry for the net connection without the VPN (WiFi or Ethernet or 4G) and another entry for the VPN connection. Which DNS servers are really being used by the OS when not running a web browser? See nslookup above.
This command can also useful after closing a VPN connection. I have seen VPN software that did not reset the DNS servers correctly when shut down. This left the computer using the DNS servers from the VPN company even when the VPN software was not running.
macOS offers the scutil -dns command. Look for nameserver. The website ss64.com offers full command syntax.
Linux should offer the nmcli command. Its output contains various sections, including "DNS configuration". See its man page.
On both Linux and macOS, you can also use the dig command to see which DNS server is being used.
On macOS, do Applications -> Utilities -> Terminal
For Linux see How to Use the dig Command on Linux by Dave McKay (April 2020).
A simple
dig somedomain.com
command should display the DNS server used to answer the question. Look for "SERVER:" in the output.
I am not an iOS developer, but from what I have read about DNS on iOS it is far too complicated for non-developers to understand. Perhaps the best support for this opinion, is a video for iOS developers, Enable encrypted DNS, where the description says "... enable encrypted DNS within an app using standard networking APIs..." So, if each app can have its own DNS configuration, what testing/checking could anyone do? Also, in my blog on VPNs on iOS are a scam, I noticed iOS 15.6 making normal old UDP port 53 DNS requests to the router despite its being configured to use NextDNS system-wide. iOS does not fully honor the system wide DNS setting. There is much more on this in the DNS Long Explanation (click at the top of the page).
DNS IS COMPLICATED
It is commonly thought that if the Operating System specifies DNS servers (either for Ethernet or for a specific SSID) they will get used. This is not always the case. Some routers (such as the Pepwave Surf SOHO) can force clients to use the DNS servers specified in the router. Worse, if the router is doing this (at least with Peplink routers) the computer can not tell. The DNS server the computer sees is not the one really being used.
This means that the DNS server reported by nslookup can not be trusted. In the first screen shot above, it looks like Windows is using 9.9.9.9 for DNS resolution. But, if Windows is configured to use 9.9.9.9 and the router is configured to use 1.1.1.1 (for example) and the router is imposing its will on all the attached devices, nslookup will report that it is using 9.9.9.9. It is not lying on purpose, it is being faked out by the router. The packets leaving the WAN port of the router will be sent to 1.1.1.1. I learned this the hard way, by doing pcap traces of data packets leaving the WAN port. I assume the same is true with the dig command on Linux and macOS.
That said, my experience has been that a router forcing the use of its DNS servers, only applies to old DNS. Browsers that specified DoH or DoT secure DNS servers had their requests honored because, to the router, a secure DNS request is a totally different thing than an old DNS request.
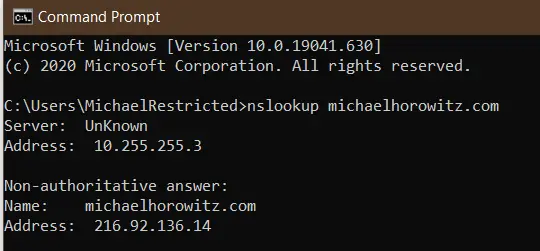
And, of course, a VPN complicates this further. Below is a screen shot of nslookup done while a Windows 10 computer was connected to a VPN. In this case, nslookup returns the IP address of the DNS server on the internal network of the VPN provider (10.255.255.3). The server is not unknown, just its name is.
Windows users can trace all instances of legacy DNS using two free and portable programs from Nir Sofer: DNSQuerySniffer (see a screen shot) and DNSLookupView. Each has its own pros/cons. If you run these programs before starting up a browser, you will see the browser making old (not secure) DNS requests to find the Secure DNS server. If things are working as they should, the only browser DNS requests, visible to Windows, are those for the Secure DNS server itself. Another idea is to run these programs with nothing going on, and see where Windows is phoning home to. I did this in October 2021 and found Windows 10 logging many actions in the System Settings app. And, you can use DNS to block Windows from being able to log your actions.
Still another approach, for Windows, was suggested by Sergiu Gatlan in his August 2020 article Microsoft adds Windows 10 DNS over HTTPS settings section. He suggests using the pktmon command to trace all activity on TCP/IP port 53. The pktmon command can not display just outgoing requests, it always includes the replies too, so it generates a lot of activity in the command window. But, it will confirm the use of old DNS. The commands Gatlan suggests are:
pktmon filter remove
pktmon filter add -p 53
pktmon start --etw -l real-time
I suggest first doing a pktmon filter list just to see if any filters are active. The logging can be stopped with Ctrl+C.
On a completely different level, you can run a very comprehensive and very technical DNS report at DNS Test Report. This report is for people who have their own domain and want to insure that the DNS environment for the domain is correctly configured. While the main audience for this report is, no dobut, networking nerds, it can also be useful as an audit for non-technical people who are paying someone else to configure their domain and/or website.
SAD DNS
A new attack on DNS servers, called SAD DNS was made public in November 2020. The attack tries to poison the DNS results, that is, pointing victims to a malicious server at the wrong IP address for a domain. The attack was created by six academics at the University of California, Riverside and at Tsinghua University. See their paper and slides.
You can test if you are using a vulnerable DNS server using the "Click to check if your DNS server is affected" link on the SAD DNS page. They warn, however, that their test is not 100% accurate.
On November 12, 2020 I ran some tests. Cloudflare, Google and Quad9 were all vulnerable. The DNS from my VPN provider was not. NextDNS initially could not resolve the SAD DNS page. The log showed that it was blocking saddns.net because it was a newly registered domain. No big deal to white list the domain. NextDNS was also reported as vulnerable.
Why Bother
Hacking a router and changing the DNS servers is a very popular type of attack. Some reports in the news:
- Brazil is at the forefront of a new type of router attack by Catalin Cimpanu for ZDNet July 12, 2019
- Website drive-by attacks on routers are alive and well. Here’s what to do by Dan Goodin July 11, 2019
- NCSC Issues Alert About Active DNS Hijacking Attacks by Ionut Ilascu for Bleemping Computer July 14, 2019
- Ongoing DNS hijackings target Gmail, PayPal, Netflix, banks and more by Dan Goodin of Ars Technica April 5, 2019
And...
iOS added encrypted/secure DNS in version 14. As of May 2022, they don't yet seem to have all the bugs out. iOS sometimes issues a warning "This network is blocking encrypted DNS traffic." I have seen it myself on iOS 15.5, and read a number of articles about how to get rid of the error message. No one knows what causes it. No one. One suggestion to get rid of the message is to forget the current SSID and re-connect to it. To me, that points to this being a bug. More here: How to Fix 'Network Blocking Encrypted DNS Traffic' on iPhone by Tim Brookes (May 2022).
Warning to Windows users: There is a caching or buffering issue involving VPNs. After connecting to a VPN, the above sites typically show both the pre-VPN DNS servers and the current DNS server from the VPN provider. On iOS 12 and Android 7.1 all the above testers work fine, only Windows is buggy. I have not tested other OSs. In the screen shot below, from the Express VPN tester page, the four OpenDNS servers were in use before the VPN connection was made and the server at Leaseweb USA is from the VPN provider. I tried the command "ipconfig /flushdns" but it did not help.
Express VPN tester while connected to a VPN
On Windows, the only tester page above that has been bullet-proof in my experience is the one for OpenDNS. It simply reports a YES/NO on whether OpenDNS is being used and it is not fooled by whatever caching issue confuses the other testers. As a side note, all the VPN services I have used assign a single DNS server. Outside of a VPN, there are normally two or more DNS servers in use.
Another issue is that different DNS testers report a different number of DNS servers. Some only report on one DNS server, others report on multiple DNS servers. I don't know why this is.
Cloudflare DNS servers are 1.1.1.1 and 1.0.0.1. In November 2018, Cloudflare released iOS and Android apps that configure those systems to use their DNS servers. It works by creating a pseudo VPN connection. The testers above do not report either 1.1.1.1 or 1.0.0.1 as the in-use DNS servers. The Cloudflare app will show that it is being used, and I am sure it is, but the above DNS testers report other IP addresses. And, you can't go by the hostname either, the servers used by Cloudflare do not have host names. The only clue from these testers is that Cloudflare is the ISP.
One feature of Cloudflare DNS is encryption. The connection between your computer and their DNS server is encrypted using one of two fairly new approaches: DNS over TLS or DNS over HTTP. This only an issue when you are not using a VPN. A VPN encrypts everything (when it is working correctly) coming and going from the computer so there is no need to pay special attention to encrypting DNS.
Warning to WIRED readers: The article You Know What? Go Ahead and Use the Hotel Wi-Fi by Brian Barrett (Nov 18, 2018) comes to a very wrong conclusion. The main point of the article is that the widespread use of HTTPS (secure websites) eliminates the old dangers of sniffing and snooping on unencrypted data. For one thing, this shows a lack of understanding of the limits of HTTPS. Secure websites do not deserve that much trust. Still, the bigger danger is that on a public wireless network you have an encrypted connection to bad guys. HTTPS does nothing to protect you from a scam website that looks real enough, displays the correct URL in the address bar, but whose sole purpose is to harvest passwords. Extended Validation could offer this protection, but in the real world it does not. For one thing, web browsers are constantly changing how they indicate EV vs. DV (Domain Validation). And, some browsers do not give any visual indication of the difference. And, I suspect no non-techies are even aware of the EV/DV concept in the first place. Even more insidious is using DNS not to fake out the main/displayed domain name, but to point the browser at a scam copy of included code from a third party. Many sites are compromised by including malicious code from hacked third parties. DNS means that the third party does not even need to be hacked. So, using trustworthy DNS servers, not those from hackers, a coffee shop or a hotel, is critical to computing safely. The article also ignores the issue of evil twin networks, an attack for which there is (as far as I know) no defense.
Anyone running a VPN on Windows 8 or 10 needs to be aware of a situation where DNS requests may be sent outside of the VPN tunnel. For more, see Guide: Prevent DNS leakage while using a VPN on Windows 10 (and Windows 8).
In May 2017, Trend Micro made a great point: "Unfortunately, website-based tests may not be reliable once a home router has been compromised." With that in mind, it makes sense to check with the router directly, be it with a web interface or an app, to double check the DNS servers.
Windows users have another excellent option, the DNS query sniffer program by Nir Sofer. The program is free, portable and from a trustworthy source. It simply traces DNS requests and responses. Before connecting to a VPN, tell it to examine either your Wi-Fi or Ethernet connection to confirm the program is working. Then connect to the VPN and you should see no further DNS activity. As further proof that the VPN is handling things, tell the program to examine your VPN connection (Options -> Capture Options) and you should see all your DNS requests.
(547/day over 2,083 days)