In my opinion, you are safest using both a modem and a router that you purchased on your own. That is, avoid equipment from your ISP. I say this for a number of reasons:
- The devices shipped by ISPs suffer from a general level of incompetence both in their initial configuration and ongoing maintenance. If nothing else, just the fact that an ISP would install a device with the default password, tells you everything you need to know about their interest in your security.
- Security and convenience are always at odds with each other. Most likely an ISP will configure a router for maximum convenience to cut down on tech support calls, which cost them money.
- Spying: We have seen that ISPs, at times, co-operate with spy agencies and governments. Even without outside influence, an ISP may well put a backdoor in the devices they give to their customers, if for no other reason than to make their life easier in some way. In this article, Your ISP is Probably Spying On You (Feb. 2018) Harrison Sand found his router was collecting information about LAN side devices and sending it the ISP.
- Don't be a prime target. Any router provided by an ISP to millions of customers is a prime target for bad guys and spies. More bang for the hacking buck. You are safer using a less popular device.
- Many ISPs want to implement public WiFi networks in your home and there is no reason to assume these are done securely. For my take on Comcast see Comcast XFINITY WiFi: Just say no. Cablevision is doing the same thing, which prompted Timothy Geigner to write: "This sort of news should serve to do nothing other than compel anyone who wishes to remain a Cablevision customer to buy their own router and modem". See also One in three home routers will double as a public hotspot by 2017. According to Juniper Research the term for this is a "homespot router".
- Sometimes equipment from an ISP is locked down. I have heard of cases where customers could not change a password and where the DNS servers could not be changed. I am told that in England, BT Business Hub and Sky Broadband prevent you from modifying the DNS servers and that much of France is also prevented from changing them. I ran into a Comcast-provided Arris TG1682G gateway where I could not change the LAN IP address of the box. I could change the subnet, but the router was always device number one which makes it a sitting duck for assorted router attacks.
- The ability to update the firmware may also be locked down. You should have full control over firmware updates.
- Backup: an ISP will give one device. Should it fail at an inopportune time, you will be off-line until you get them to issue a replacement. When you own your own hardware, you can buy a second modem and/or a router for emergency backup.
- It may well be cheaper in the long run to buy your own hardware
As to the last point, some ISPs charge a rental fee for the box they provide, be it just a modem or a full fledged gateway. Buying your own will pay for itself soon enough. Time Warner customers looking to buy their own modem can purchase one from this list or this one. Comcast users should review mydeviceinfo.comcast.net.
In June 2022, on a financial Forum, someone asked Which is the best (most secure) home internet router for the money?. One response hit home: "I've been on the vendor side selling networking equipment to carriers and cable companies. Their priorities for customer premises equipment (consumer) are cost, remote management and cost. Not to say their routers are bad, but you can do better." To re-phrase that, ISPs want cheap routers that they can control.
ISPs SCREWING UP
May 2, 2023: This is not about security, but it does show how little Spectrum cares about the boxes they give out to customers
'Somebody had to see that before they shipped it out': Spectrum customer receives router with a live roach colony inside by Jack Alban for Daily Dot. About a posting by TikToker user Fleur who was sent a router infested with cockroaches.
In November 2021, we learned of a DNS rebinding flaw in six million Sky routers (they are a large ISP in the U.K.). Adding insult to injury, Sky took 18 months to fix the problem and often ignored the company that found and reported the flaw, Pen Test Partners. See SkyFail. 6 million routers left exposed.
In September 2021 we learned that Virgin Media failed to fix a reported flaw in their routers for over two years. See: Virgin Media Routers Left VPN Users Vulnerable Since at Least 2019 by Nathaniel Mott for PC Magazine.
A privacy issue with IP Version 6 (IPv6) was disclosed at a BlackHat presentation in August 2021. It is not a flaw in IPv6, instead it is lazy, stupid, ignorant choices made by assorted ISPs that continue to include a MAC address as part of the public IPv6 address. We have known for 20 years that this is a bad idea. Yet, ISPs continue to do it. For the details see Your Wi-Fi router could tell everyone where you live - here's what you can do about it by Paul Wagenseil of Toms Guide. Researchers found over 12 million routers/gateways that included a MAC address (which should be private) in the public IPv6 address. In the US they found more than 1 million Comcast Xfinity gateway routers with this design flaw.
In May 2019, British ISP Sky Broadband updated their broadband hubs and knocked some customers off-line. Specifically, if the customer had configured the device to use DNS servers not from Sky Broadband. It seems the latest update also removed the ability to change DNS servers altogether. See Sky customers moan: Our broadband hubs are bricking it and read the many comments.
In December 2018, Tenable found three bugs in a Verizon FIOS router/gateway. Reading the Disclosure Timeline tells you all you need to know - not to use hardware provided by Verizon. For one thing, Verizon did not write the firmware, so they have to farm out the bug fix. Then, two bugs are dealt with by one group, while the third bug is dealt with by another group. Two bugs were already known but had not been fixed. Verizon's response was slow and bureaucratic and they have no plans to say anything publicly about the bugs.
In May 2018, we learned that Comcast website bug leaks Xfinity customer data. The Comcast website (register.be.xfinity.com/activate), which was/is used by customers to set up their home services, could be hacked to display a customers home address, Wi-Fi network name and Wi-Fi password. And, not just display, an attacker could also change the SSID and/or Wi-Fi password. But, the issue was only for customers using equipment from Comcast. Those with their own routers were safe. An attacker only need to provide the customer account number and their house or apartment number. If you lived at 123 Main Street, all the attacker needed to know was 123. Comcast claimed they fixed the problem, but we have no idea how long this vulnerability has existed.
Then, in June 2018, we learned of another data leak by Comcast. Any device on the network of a Comcast customer, could call an API and learn the account number, the customer's home address, the account type, and any services enabled on the line.
For the Love of God, Stop Renting Routers From Comcast by Karl Bode May 24 2018. On the one hand, this article brings up many different and valid points, both financial and technical. On the other hand, the author seems clueless about the difference between a router a modem and a gateway.
Talk Talk is a British ISP and telco. In May 2018, their routers were confirmed vulnerable to the classic WPS pin code attack, first seen back in 2011. You can't make this stuff up. The flaw was discovered by a company called IndigoFuzz using a Windows program called Dumpper.
Another British ISP, EE, distributes gateways (combination modem and router) with a backdoor account. This came to light in October 2018, see this article from The Register. The backdoor account in their 4GEE HH70 gateways was accessible via SSH from the LAN (inside) side of the router. Worse, when the problem was reported to EE they blew it off, until The Register got involved. Even after the bad publicity, it was still not clear whether a patch had been rolled out or not. Eventually, The Register learned that EE had issued a patch, but customers have to install the new firmware themselves.
In November 2017, a new botnet was discovered that abused flaws in ZyXEL devices. Bad guys could remotely login to the routers/gateways using a default userid/password because a port was left open. In addition, the devices also had a hard coded superuser password, which gave attackers root privileges. Roughly 100,000 infected devices were detected, almost all of them in Argentina, specifically in the network of Telefonica de Argentina. Obviously, the ISP is at fault for giving so many of their customers devices with the same passwords.
In September 2017, ESET reported that some ISPs (in two countries they refused to name) appear to be co-operating in the distribution of spyware. New FinFisher surveillance campaigns: Internet providers involved? by Filip Kafka Sept. 21, 2017. Quoting: "New surveillance campaigns utilizing FinFisher, infamous spyware known also as FinSpy and sold to governments and their agencies worldwide, are in the wild ... some of these variants have been using a cunning, previously-unseen infection vector with strong indicators of major internet service provider (ISP) involvement ... FinFisher is marketed as a law enforcement tool and is believed to have been used also by oppressive regimes ... What’s new ... in terms of distribution is the attackers' use of a man-in-the-middle attack with the "man" in the middle most likely operating at the ISP level ... When the ... target of surveillance is about to download one of several popular (and legitimate) applications, they are redirected to a version of that application infected with FinFisher. The applications we have seen being misused to spread FinFisher are WhatsApp, Skype, Avast, WinRAR, VLC Player and some others ... the legitimate download link [is] being replaced by a malicious one ... "
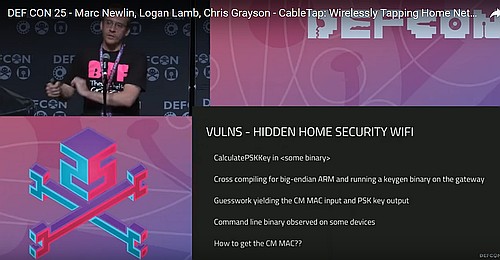 At the DEF CON 25 conference in the summer of 2017 Marc Newlin, Logan Lamb and Chris Grayson spoke about Wirelessly Tapping Home Networks. They found 26 bugs in ISP provided hardware, both gateways and set-top boxes. Bugs were found in devices from Cisco, Arris, Technicolor, Motorola and Xfinity. They found multiple un-authenticated remote code execution flaws, the worst of all possible bugs. Software maintenance of the devices was also poor: patches take months to deploy, official bug reports are not filed and, of course, customers (victims?) are told nothing about the problems.
At the DEF CON 25 conference in the summer of 2017 Marc Newlin, Logan Lamb and Chris Grayson spoke about Wirelessly Tapping Home Networks. They found 26 bugs in ISP provided hardware, both gateways and set-top boxes. Bugs were found in devices from Cisco, Arris, Technicolor, Motorola and Xfinity. They found multiple un-authenticated remote code execution flaws, the worst of all possible bugs. Software maintenance of the devices was also poor: patches take months to deploy, official bug reports are not filed and, of course, customers (victims?) are told nothing about the problems.
"Securing home routers is not an easy task and may require some technical knowledge. A good start is properly selecting a home router - this means avoiding free routers included in internet plans... " from Securing Your Home Routers by Trend Micro sometime in 2017.
In December 2016, Scott Helme wrote My Ubiquiti Home Network about upgrading from consumer routers to Ubiquiti. But, he lead with his thoughts about ISP provided equipment.
"I've never used the equipment provided by my ISP and have always used my own ... I've always been a bit of a tech geek and I like having things with extra features ... but there are some other more genuine needs. ISP (Internet Service Provider) provided equipment usually has one main factor driving the choice of hardware, cost. They want it to be as cheap as possible because purchasing the device and giving it to you is eating into their profits ... low cost usually means low quality in other areas than hardware too, like security. My previous ISP, EE, sent me a BrightBox router when I signed up that [had] several serious security vulnerabilities ... Following their (very late) patching efforts there were yet more vulnerabilities. I could go on and on listing the issues with ISP kit, a story even popped up on The Register about 1 million German routers being compromised whilst writing this blog, but I think you get the idea. This isn't to say other hardware will be perfect, of course it won't be, but I'd seen enough and wanted rid."
In Australia in October 2016 an ISP gave out routers with default userid/passwords and "remarkably similar SSIDs." The article argues that: "It isn't terribly difficult to load up factory firmware that generates a random password, assigns it to a device, then prints a label with that information to go into the box with the gadget. It's more work than just slapping a default username and password into the software - but not much. And the cost, amortised against tens of thousands of units, can't be more than a penny or two."
Lucian Constantin, of IDG News Service, has been covering routers for Computerworld, PC World and others for a few years. On June 2, 2015, writing in ITworld, about a bunch of router flaws he said:
"Past research has shown that the security of ISP-provided routers is often worse than that of off-the-shelf ones. Many such devices are configured for remote administration to allow ISPs to remotely update their settings or troubleshoot connection problems. This exposes the routers' management interfaces along with any vulnerabilities in them to the Internet, increasing the risk of exploitation. Even though ISPs have the ability to remotely update the firmware on the routers they distribute to customers, they often don't and in some cases the users can't do it either because they only have restricted access on the devices."
In Nov. 2015 Bernardo Rodrigues wrote ARRIS Cable Modem has a Backdoor in the Backdoor. The buggy devices are the Arris TG862A, TG860A, and DG860A. To be clear, these are not modems, they are gateways (combination modem and router). They suffer from XSS and CSRF vulnerabilities, hard-coded passwords, and a backdoor in a backdoor. The backdoor can be used to enable Telnet and SSH remotely via a hidden HTTP interface or with custom SNMP MIBs. Estimates are that more than 600,000 externally accessible devices are vulnerable. Initially, Arris blew this off. Eventually CERT/CC was able to get their attention. For more, see the Router Bugs page under November 2015.
Verizon was giving new customers routers configured to use WEP years and years and years after WEP was known to be insecure. It's nice to be a monopoly. In November 2014 the FTC wrote a letter to a Verizon rep saying "... the Division of Privacy and Identity Protection has conducted an investigation into possible violations of Section 5 of the Federal Trade Commission Act by ... Verizon Communications. The investigation considered whether Verizon engaged in unfair or deceptive acts or practices by failing to secure, in a reasonable and appropriate manner, the routers it provided to its High Speed Internet (DSL) and FiOS customers ... Verizon regularly shipped routers to consumers with the default security set to an outdated encryption standard known as WEP. Due to certain weaknesses in WEP, the IEEE deprecated this standard in 2004 in favor of a new standard known as WPA and later, WPA2. However, until recently, Verizon continued to ship some router models with the WEP encryption standard. As a result, many Verizon customers ... [are] vulnerable to hackers." Writing the letter was all the FTC did. Clearly you can't trust Verizon with your router security.
TR-069
Another big security issue involves remote configuration of the router/modem provided by an ISP. Assorted mechanisms used by ISPs to update their devices in your home or office have been abused by bad guys to hack the devices. One remote update mechanism is a protocol with two names: TR-069 and CWMP. More than once, bugs in this protocol have been abused.
In November 2016, about 900,000 customers of Deutsche Telekom were knocked off-line by router problems. My blog on this attack, which started with a new variant of the Mirai malware, detailed the mistakes ISPs made to get to the point where Mirai could cause so much damage. They left an open TCP/IP port undefended, and then quickly blocked it once the s..t hit the fan. Some ISP-supplied routers were running a TR-064 server that was open to the public, a huge configuration mistake. And, some routers locked up when the had to deal with the many incoming connection attempts created by the malware.
Another example of TR-069 incompetence came to light in April 2017. Wordfence wrote that "Your ISP should not allow someone from the public internet to connect to your router's port 7547." Well, duh. They wrote that Shoden reports over 41 million home routers with port 7547 open to the public internet. They also found over 10,000 infected home routers in Algeria and over 11,000 hacked home routers in India that they attribute to port 7547 being open.
TR-069 was also abused in 2014. A story, by Lucian Constantin back in August 2014 is frightening. See Home routers supplied by ISPs can be compromised en masse. As of 2011, there are 147 million TR-069-enabled devices online listening on TCP port 7547. These devices communicate with Auto Configuration Servers (ACS) operated by ISPs for assorted network management tasks. Many times a router can not close the port. If an attacker hacks into an ACS server then lots of bad stuff can happen. According to Shahar Tal, a security researcher at Check Point Software, ACS servers can be easily taken over by bad guys. The TR-069 specification recommends the use of HTTPS but he found that insecure HTTP is used about 80 percent of the time, opening routers up to man-in-the-middle attacks. TR-069 requires authentication from the device to the ACS, but the username and password is typically shared and easily extracted. Check Point also tested several ACS servers and found critical remote code execution vulnerabilities in them.
Open ports on ISP provided hardware are not limited to the TR-069 protocol. In September 2017, security firm Nomotion blogged about AT&T U-Verse gateway devices with two open ports. One was for SSH, the other (TCP port 49152) allowed WAN side attackers to bypass the firewall. This was in addition to three hard coded backdoor accounts they discovered. The blog has a great title: SharknAT&To. Adding insult to injury, was the reaction from AT&T. Despite being publicly shamed, they said nothing about these security problems for two weeks (as of Sept 13, 2017). They have no shame and are doing their best to keep their customers ignorant of this. Arris, said they are looking into it and then went silent. For more see the Router Bugs page under September 2017.
HD Moore, chief security architect at Rapid7, and the creator of Metasploit, also weighed in on this on June 17, 2015. Rapid7 runs Project Sonar, which scans the Internet for vulnerable devices. They find that things are getting worse. On reason, cited by Moore is "that a few dozen Internet service providers are rolling out broadband devices such as home routers without properly vetting or properly configuring the security..."
------------------
Besides security, there is the issue of honesty. Time Warner Cable, a.k.a Spectrum and Charter was sued in New York State in early 2017 for lying about the download speeds their customers were getting. In The Alternate Facts of Cable Companies Harvard professor Susan Crawford writes:
"Based on the company's own documents and statements, it appears that just about everything it has been saying since 2012 to New York State residents about their internet access and data services is untrue. And not untrue in some grey, shadowy way - just untrue. The company's 2.5 million New York subscribers (of its 22 million nationwide) have been told they are getting X (in terms of download and upload speeds) when actually they are getting a lot less than X."
How was Charter/Spectrum/Time Warner Cable cheating? Three ways: " ... squeezing more households into an inadequate number of narrow, shared neighborhood data connections; squeezing connections between Spectrum's network and other networks; and squeezing consumers who should have gotten upgraded household equipment."
The lawsuit was settled in December 2018 with Charter/Spectrum coughing up $176 Million. In an article about this, Karl Bode, of Techdirt wrote: "The suit also highlights how Charter at least considered gaming the results of a program the FCC has traditionally used to measure real-world broadband speeds using custom-firmware embedded routers in consumer volunteer homes.".In the U.S., high speed broadband is pretty much a monopoly everywhere. An ISP without competition has no motivation to do a good job, they are only motivated by profit. Yet another reason not to use their hardware, when possible.
One advantage of the new consumer focused mesh routers, like eero, AmpliFi and Google Wifi, is that the routers themselves can run speed tests. Eero seems to do one every day. AmpliFi and Google Wifi keep a history of the speed tests, so trends are easily spotted. Eero does not keep a history.
Finally, there is a big difference between routers so don't expect to buy the perfect router for your needs right out of the box. If possible, buy a router from a place that will take it back.